Programming
The AEPOC has the ability to dynamically compile small user programs and run them to allow users to extend the core functionality or provide some alarm handling that we have not provided in the core software. All are fixed length, with some stroke and timed programs longer and the alarm and event action programs much smaller. Since they are compiled to byte code and interpreted, they don't run as fast as the core software does, but the size of the programs limits the impact on the controller itself.
If end users report the programs to us and request their evaluation to be included in the core software and available to all users, we will consider them based on the perceived usefulness to a wide range of customers, ease of incorporation, and lack of impact on other existing features of the software.
These screens allow the user to upload the current program from the AEPOC, edit it, save it to disk, and download it to the AEPOC. Existing programs can also be loaded from disk and downloaded to the AEPOC.
Users running their own programs take responsibility for ensuring that program loops don't impact the operation of the controller. Most user programs end up just executing a series of if statements and altering parameters based on the current state of the controller and run little risk of impacting the operation unless they specify a wrong parameter to change.
Stroke program
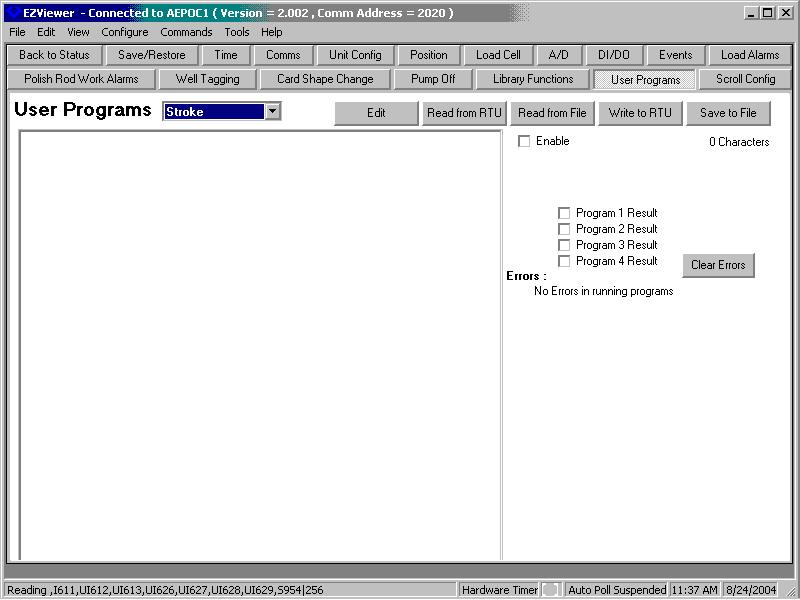
The stroke program runs once per stroke. There is a similar program that runs once per cycle, but it isn't shown here since it is similar.
Time based programs
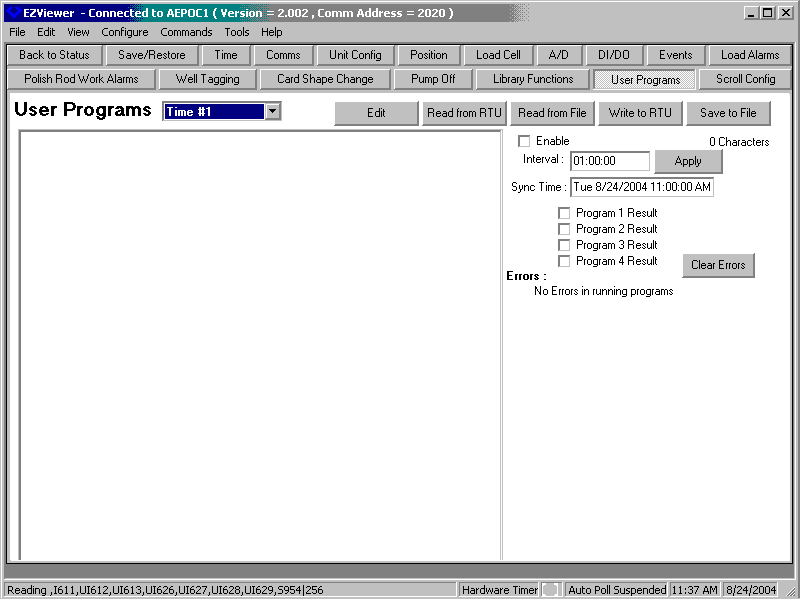
Time based programs are similar to stroke programs but run at a particular time interval. There are two time based programs available.
Alarm programs
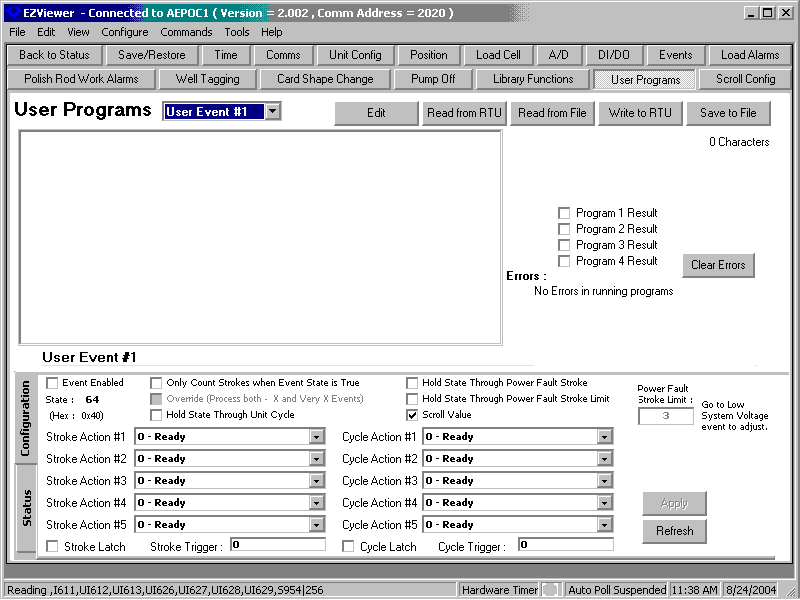
There are four user defined alarm programs that exist. These are used to set a particular alarm register to true or false based on the state of other registers in the controller. These then are used by the alarm processing software in the controller to take the usual stroke or cycle based actions if true.
The analyst can also specify up to sixty four separate very small programs to run as one of the five event stroke or cycle actions or by command from the host or user. These typically configure registers in particular ways to perform some special processing or zero other registers due to some external stimulus.